GEM88 ⚜️ LINK VÀO GEM888 MỚI NĂM 2025【usa-vpn.net】

Gem88 là điểm hẹn giải trí trực tuyến đang tạo sức hút mạnh mẽ trong cộng đồng nhờ sự kết hợp giữa công nghệ hiện đại và trải nghiệm chơi game đỉnh cao. Đây là một sân chơi đa dạng với giao diện mượt mà, kho game phong phú và tỷ lệ thưởng hấp dẫn. Người chơi không chỉ được thỏa mãn niềm đam mê giải trí mà còn cảm nhận rõ sự an toàn, minh bạch trong từng giao dịch.
Giới thiệu sơ lược về nhà cái cá cược Gem88
Giới thiệu Gem88 là một trong những thương hiệu cá cược trực tuyến nổi bật làng cược. Điểm cộng lớn của nhà cái Gem88 nằm ở kho game phong phú bậc nhất thị trường.
Nguồn gốc hành thành
Đơn vị đã được ghi danh vào European Parliament and Commission Transparency Registry với số giấy phép C-39017 kể từ tháng 10/2016. Hiện nay, đây là thành viên trực thuộc Hiệp hội Cá cược và Trò chơi châu Âu (EGBA), đồng thời được cấp phép hoạt động hợp pháp bởi PAGCOR – cơ quan quản lý cá cược uy tín tại Philippines. Hệ thống nhanh chóng khẳng định vị thế khi mang đến cho người chơi không gian giải trí minh bạch, an toàn và công bằng nhờ nền tảng pháp lý vững chắc.
Mục tiêu hoạt động
Người chơi có thể trải nghiệm hàng ngàn kèo cược thể thao mỗi ngày, từ Premier League, La Liga cho đến Champions League. Ngoài ra, nhà cái còn đem đến thế giới casino trực tuyến đẳng cấp với Baccarat, Blackjack, Roulette, Sicbo, cùng các dealer chuyên nghiệp trực tiếp mang đến trải nghiệm chân thực. Đặc biệt, với các game bài quen thuộc như Tiến Lên Miền Nam, Phỏm, Mậu Binh hay Poker, đơn vị luôn đáp ứng mọi sở thích, giúp người chơi không bao giờ nhàm chán.
Slogan “Trải nghiệm cá cược hoàn hảo” không chỉ là lời hứa mà còn là phương châm hoạt động của đơn vị. Nhà cái này luôn đặt lợi ích hội viên lên hàng đầu, liên tục cập nhật và nâng cấp hệ thống để mang lại trải nghiệm mượt mà. Đội ngũ tác giả Gem88 chuyên nghiên cứu để cho ra các bài viết, hướng dẫn chuyên sâu.
Link vào Gem88 mới nhất
Để tham gia trải nghiệm cá cược trực tuyến mượt mà, người chơi cần truy cập link vào Gem88 mới nhất. Hiện tại, đường dẫn chính thức được cập nhật là https://usa-vpn.net/. Đây là cổng vào bảo mật, giúp bạn kết nối nhanh chóng mà không lo bị chặn hay gián đoạn. Chỉ với một cú nhấp chuột, anh em đã có thể mở ra thế giới game đa dạng, từ nổ hũ, tài xỉu cho đến cá cược thể thao đỉnh cao.
Điểm đặc biệt của link Gem88 này là luôn được cập nhật liên tục, tránh tình trạng lỗi truy cập thường gặp. Nhờ đó, người chơi hoàn toàn yên tâm tận hưởng các trận game nảy lửa mà không bị gián đoạn giữa chừng. Bên cạnh đó, giao diện thân thiện, tốc độ tải nhanh cũng mang lại trải nghiệm siêu mướt dù bạn dùng điện thoại hay máy tính.
Điểm danh kho game chất lượng cao tại nhà cái
Khi nhắc đến Gem88, anh em không chỉ tìm thấy một sân chơi cá cược uy tín mà còn được trải nghiệm cả một kho game đồ sộ với đủ thể loại hấp dẫn. Mỗi sảnh cược tại đây đều được đầu tư chỉn chu, đảm bảo vừa dễ chơi vừa dễ thắng, mang đến cảm giác giải trí đúng nghĩa cho người chơi Việt. Dưới đây là những mảng game nổi bật nhất mà bạn có thể khám phá ngay hôm nay.
Thể thao
Hệ thống mang đến sảnh thể thao cực chất, bao phủ từ bóng đá, bóng rổ, tennis cho đến eSports. Người chơi có thể theo dõi tỷ lệ kèo minh bạch, cược trực tiếp từng phút với đường truyền nhanh, không giật lag. Từ những giải đấu lớn như Ngoại Hạng Anh, Champions League đến các trận khu vực, tất cả đều có mặt đầy đủ để anh em thỏa sức dự đoán.
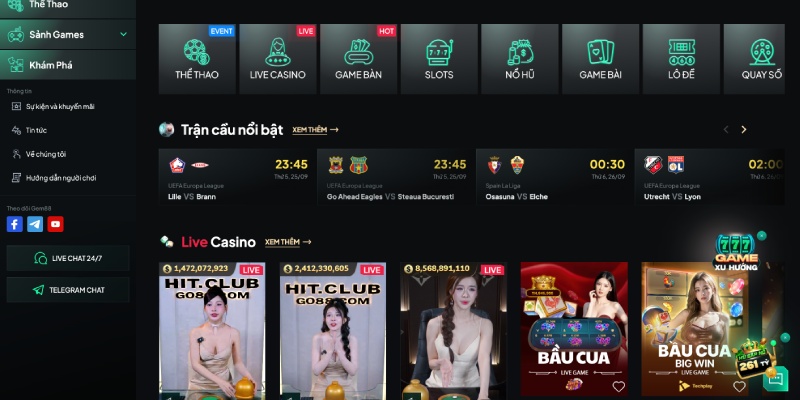
Livecasino
Nếu bạn muốn cảm nhận không khí sòng bài thật, Livecasino Gem88 chính là lựa chọn không thể bỏ lỡ. Dealer xinh đẹp, bàn chơi trực tuyến rõ nét full HD, kết hợp đa dạng game như Baccarat, Rồng Hổ, Roulette… Tất cả tạo nên trải nghiệm như đang ngồi giữa casino hạng sang nhưng ngay trên màn hình điện thoại.
Nổ hũ
Nổ hũ Gem88 luôn nằm trong top game ăn khách nhất. Tỷ lệ nổ hũ cao, vòng quay mượt mà, đồ họa sinh động khiến mỗi lượt quay đều hồi hộp. Game thủ dễ dàng săn hũ lớn chỉ với vốn cược nhỏ, từ đó tạo nên cơ hội đổi đời hấp dẫn. Nhiều chủ đề slot machine mới lạ được cập nhật liên tục, không lo nhàm chán.
Game bài
Kho game bài Gem88 đúng chuẩn thiên đường cá cược đa dạng. Anh em có thể chơi Tiến Lên, Phỏm, Poker, Mậu Binh, Liêng… với luật chơi rõ ràng, giao diện đẹp mắt. Chơi với người thật, đặt cược minh bạch và tỷ lệ trả thưởng cao chính là điểm cộng lớn giúp nhà cái ghi dấu ấn trong lòng bet thủ.
Xổ số – Lô đề
Đối với fan đam mê con số, trang chủ Gem88 tích hợp đầy đủ xổ số truyền thống và lô đề online. Người chơi dễ dàng chọn số, đặt cược nhanh chóng, nhận kết quả tức thì. Hệ thống cam kết minh bạch, trả thưởng đúng kỳ, giúp anh em yên tâm thử vận may mỗi ngày.
Lý do hàng triệu hội viên lựa chọn Gem88
Nếu anh em đang tìm kiếm một sân chơi uy tín, kho game đa dạng và chất lượng cao, thì Gem88 chính là lựa chọn sáng giá. Tại đây, người chơi không chỉ được trải nghiệm hàng trăm tựa game hot mà còn yên tâm nhờ hệ thống vận hành minh bạch, luật lệ rõ ràng. Cùng điểm qua những ưu điểm nổi bật giúp nhà cái trở thành địa chỉ giải trí được đông đảo bet thủ tin chọn.
Sân chơi uy tín rõ ràng
Điều khoản và điều kiện được công khai minh bạch, thể hiện rõ cam kết của nhà cái luôn lấy sự minh bạch làm tiêu chí số một. Tất cả các trò chơi, từ cá cược thể thao, casino đến nổ hũ đều đi kèm điều khoản và điều kiện chi tiết. Điều này giúp người chơi hiểu rõ quyền lợi, nghĩa vụ cũng như hạn chế những tranh chấp không đáng có. Với sự rõ ràng ngay từ đầu, game thủ dễ dàng nắm bắt luật chơi và an tâm trải nghiệm.
Chính sách bảo mật chặt chẽ
Một trong những điểm cộng lớn tại Gem88 chính là chính sách bảo mật nghiêm ngặt. Toàn bộ thông tin cá nhân và giao dịch tài chính của người chơi đều được mã hóa hiện đại, đảm bảo an toàn tuyệt đối. Nhờ đó, game thủ có thể tập trung vào cá cược mà không lo bị lộ dữ liệu hay mất quyền kiểm soát tài khoản.
Giao diện xịn
Gem88 thiết kế nền tảng với giao diện hiện đại, bố cục mạch lạc, giúp người mới cũng có thể thao tác nhanh chóng. Các danh mục game được phân chia rõ ràng, tính năng tìm kiếm tiện lợi, mang đến trải nghiệm liền mạch từ PC cho đến điện thoại.
Kho game chất
Hệ thống sở hữu một kho game đồ sộ gồm hàng loạt sảnh cá cược, slot game, live casino và lô đề. Đặc biệt, tỷ lệ trả thưởng luôn hấp dẫn, giúp người chơi có cơ hội săn jackpot lớn chỉ với vốn nhỏ. Đây chính là lý do khiến nhiều bet thủ gắn bó lâu dài cùng nhà cái.
Hỗ trợ khách hàng tận tâm
Ngoài kho game chất lượng, Gem88 còn ghi điểm nhờ dịch vụ chăm sóc khách hàng chuyên nghiệp. Hệ thống chăm sóc khách hàng hoạt động 24/7, luôn túc trực để hỗ trợ và giải đáp mọi câu hỏi của bạn, từ khâu nạp tiền cho đến các vấn đề khác với nhiều phương thức liên hệ. Anh em có thể yên tâm vì luôn có “người đồng hành” trong suốt quá trình trải nghiệm.
Hướng dẫn tân binh gia nhập hệ thống Gem88
Gia nhập Gem88 chưa bao giờ dễ dàng và thú vị đến thế. Nhà cái này thiết kế mọi quy trình cho người chơi mới theo phong cách dân dã, gọn nhẹ nhưng vẫn đầy đủ tính năng cần thiết. Nếu bạn là tân binh muốn hòa mình vào thế giới cá cược, chỉ cần vài bước cơ bản là có thể bắt đầu ngay hành trình săn thưởng.
Đăng ký tài khoản nhanh gọn
Điểm khởi đầu là thao tác đăng ký tài khoản Gem88. Giao diện được tinh giản, các mục điền thông tin rõ ràng, dễ hiểu, chỉ mất tầm 2 phút là xong. Người chơi chỉ cần cung cấp số điện thoại, email và mật khẩu an toàn, hệ thống sẽ gửi mã xác nhận để kích hoạt ngay lập tức. Không rườm rà, không vòng vo – đúng chất thân thiện cho tân binh.
Nạp tiền
Sau khi có tài khoản, bước tiếp theo là nạp tiền vào Gem88. Nhà cái hỗ trợ đa dạng kênh giao dịch: ngân hàng nội địa, ví điện tử, QR Pay… với tốc độ xử lý gần như tức thì. Tân binh không phải lo lắng vì luôn có hướng dẫn chi tiết kèm theo. Hơn nữa, các giao dịch đều được mã hóa chuẩn quốc tế, bảo mật thông tin tuyệt đối.
Khuyến mãi Gem88 ngập tràn ưu đãi
Khuyến mãi Gem88 luôn biết cách chiều lòng người chơi bằng hàng loạt chương trình ưu đãi hấp dẫn. Từ quà tặng chào mừng tân binh đến hoàn trả hàng ngày, tất cả đều được thiết kế để anh em có thêm vốn liếng và trải nghiệm chơi game thoải mái hơn. Nếu bạn đang tìm kiếm một sân chơi vừa vui vừa có lợi, loạt ưu đãi sau đây chắc chắn sẽ khiến bạn mê mẩn.
Thành viên mới +100,000 VNĐ
Ngay khi đăng ký tài khoản tại Gem88, bạn sẽ được tặng thưởng 100,000 VNĐ cực dễ dàng. Chỉ cần:
- Nạp tối thiểu 300,000 VNĐ.
- Xác thực Telegram hoặc số điện thoại.
- Vào mục khuyến mãi, chọn đúng ưu đãi và kiểm tra điều kiện.
- Nếu đủ, bấm ngay “Nhận 100K” để tiền thưởng chảy thẳng vào ví.
Lưu ý, đây là phần quà dành riêng cho thành viên mới. Để rút thưởng, bạn chỉ cần hoàn thành mức cược tối thiểu 1,000,000 VNĐ. Tuy nhiên, chương trình sẽ không áp dụng cho một số trò như Tài Xỉu, Baccarat, Long Lân Quy Phụng, Mini Game, Esports, Xóc đĩa Techplay… Anh em nhớ đọc kỹ trước khi tham gia để không bỏ lỡ quyền lợi.
Khuyến mãi chào mừng người chơi mới tại Gem88
Đặc quyền tiếp theo chính là ưu đãi nhân đôi tiền nạp lần đầu. Khi bạn đăng ký tài khoản và nạp lần đầu, Gem88 sẽ tặng thêm 100% giá trị tiền nạp, tối đa lên tới 15,000,000 VNĐ.
Ví dụ: nạp 1,000,000 VNĐ, bạn nhận ngay 1,000,000 VNĐ thưởng → tổng vốn chơi là 2,000,000 VNĐ. Tuy nhiên, để rút tiền, bạn cần hoàn thành mức cược theo công thức: (tiền nạp + tiền thưởng) × 25. Nghĩa là với 1 triệu nạp + 1 triệu thưởng, tổng cược cần đạt là 50 triệu VNĐ.
Tùy từng thể loại game, tỷ lệ tính cược khác nhau:
- Thể thao: 100%.
- Lô đề: 50%.
- Nổ hũ, Bắn cá, Keno, Number Game: 25%.
- Esports, Thể thao ảo, Live Casino, Mini Game…: 0%.
Đây là cơ hội vàng cho người mới “có vốn to” ngay từ lần đầu nhập cuộc.
Hoàn trả 1.3% không giới hạn
Điểm cộng lớn của Gem88 chính là chính sách hoàn trả 1.3% mỗi ngày. Không giới hạn mức hoàn, hệ thống sẽ tự động cộng vào tài khoản lúc 13h00 dựa trên tổng cược hợp lệ ngày hôm trước.
Cách tính tỷ lệ hoàn trả:
- Thể thao, Thể thao ảo: 100% tiền cược.
- Lô đề: 50% tiền cược.
- Keno, Quay số, Bắn cá, Nổ hũ, Spribe…: 25% tiền cược.
- Game bài, Sòng bài, Mini Game, Esports…: Không tính tiền cược.
Ngoài ra, những vé cược hòa, hủy hoặc cược dưới tỷ lệ cho phép (ví dụ DEC odds <1.5) sẽ không được tính vào tổng cược. Người chơi chỉ được chọn 1 chương trình khuyến mãi tại một thời điểm, nên hãy cân nhắc chọn khôn ngoan để tối đa lợi ích.
Các câu hỏi thường gặp (FAQ) về nhà cái Gem88
Khi tham gia cá cược tại nhà cái Gem88, chắc chắn anh em sẽ có nhiều thắc mắc từ cách đăng ký, nạp tiền, rút tiền cho đến bảo mật thông tin. Để giúp người chơi mới và cả hội viên lâu năm tiết kiệm thời gian, dưới đây là những câu hỏi thường gặp nhất kèm câu trả lời chi tiết, dễ hiểu và thực tế.
Cách thức tạo tài khoản tại Gem88 ra sao?
Việc đăng ký cực kỳ nhanh chóng, chỉ cần truy cập link chính thức của nhà cái Gem88, chọn mục Đăng ký, sau đó điền đầy đủ thông tin như tên đăng nhập, mật khẩu, số điện thoại hoặc email. Ngay khi hoàn tất xác minh, hệ thống sẽ kích hoạt tài khoản của bạn tức thì. Anh em nhớ đọc kỹ điều khoản và điều kiện trước khi hoàn tất để đảm bảo quyền lợi của mình.
Hệ thống hỗ trợ những phương thức nạp và rút tiền nào?
Đơn vị mang đến nhiều lựa chọn tiện lợi như chuyển khoản ngân hàng, ví điện tử và thẻ cào. Hệ thống xử lý nhanh chóng, nạp tiền chỉ mất vài phút còn rút tiền thường hoàn tất trong vòng 30 phút – 2 giờ. Người chơi cần lưu ý xác minh thông tin cá nhân để giao dịch trơn tru và tuân thủ đúng chính sách bảo mật của nhà cái.
Tiền thưởng khuyến mãi tại gem88 có rút được không?
Có, nhưng người chơi cần đáp ứng đủ yêu cầu về vòng cược (rollover) theo từng chương trình khuyến mãi. Ví dụ, nếu nhận thưởng 100K khi đăng ký mới, bạn phải cược tối thiểu một mức nhất định thì mới có thể rút. Tất cả chi tiết đều được nêu rõ trong phần thể lệ khuyến mãi mà nhà cái công bố. Anh em nên đọc kỹ để tránh bỏ sót quyền lợi, mọi vấn đề phát sinh do hội viên nhà cái sẽ miễn trừ trách nhiệm.
Kết luận
Gem88 không chỉ dừng lại ở việc mang đến một kho game đa dạng và nhiều ưu đãi hấp dẫn, mà còn tạo dựng cho người chơi một sân chơi an toàn, minh bạch và đầy trải nghiệm mới lạ. Với giao diện mượt mà, chính sách bảo mật chặt chẽ cùng hệ thống chăm sóc khách hàng tận tâm, hệ thống ngày càng khẳng định vị thế là địa chỉ cá cược đáng tin cậy trong lòng cộng đồng.